Beware of MalDoc in PDF: A New Polyglot Attack Allowing Attackers to Evade Antivirus
By TheHakerNews.com
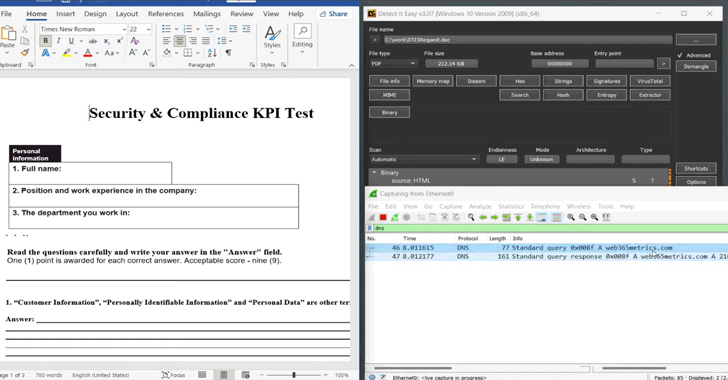
Cybersecurity researchers have called attention to a new antivirus evasion technique that involves embedding a malicious Microsoft Word file into a PDF file.
The sneaky method, dubbed MalDoc in PDF by JPCERT/CC, is said to have been employed in an in-the-wild attack in July 2023.
“When a document is downloaded from the internet or email, it’ll carry a MotW,” security researcher Will Dormann said. “As such, the user will have to click ‘Enable Editing’ to exit Protected View. At which point they’ll be learn [sic] that macros are disabled.”
While real-world attacks leveraging MalDoc in PDF were observed a little over a month ago, there’s evidence to suggest that it was being experimented (“DummymhtmldocmacroDoc.doc“) as early as May.
Read more: https://thehackernews.com/2023/09/beware-of-maldoc-in-pdf-new-polyglot.html
